Many discussions around data security include the issue of data encryption. If you are sending commercially important information like banking data or electronic payments over the web it is safe to assume that this data transmission is encrypted because the tools which are commonly used for this type of transaction incorporate the protocols needed. 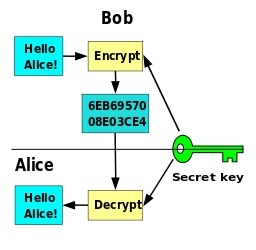
What about other date you might transmit, like invoice records being stored on a cloud based storage system or employee records placed online in a storage file? Are these types of transmissions encrypted?
What about information like price lists or other critical corporate data which is stored on an employees laptop or other mobile device? Are these files encrypted so that if the device is stolen or misplaced this important corporate information can't be accessed.
What about customer data which relates to their confidential business with your organization? How damaging would its disclosure be to your relationship and to their business.
These are just a few examples of the types of information that you might want to think about when the question of encryption is considered.
How hard is it?
There are many ways that you can decide to undertake an encryption protocol. All of them will include deploying some sort of encryption software which can undertake the hard work of converting raw files to encrypted versions and then being able to convert them back to readable format when needed. Deciding on what to deploy is somewhat like making any other software purchase. Research a few commercially available solutions, talk to other business advisors or colleagues and then test a couple of samples for ease of use, reliable handling and ease of access when data is needed.
The next step it to decide what has to be encrypted and what steps will be put in place to ensure it is done. Of course using the right procedures to protect against the disclosure of the retrieval tools is also important. Having the retrieval key nicely taped to the laptop so anyone can open one of the encrypted files or the whole hard drive is not going to be a good idea. Making sure users and employees protect this type of tool is as important and potentially even more important than protecting passwords and login info.
relevant discussions
Canadian firms not using encryption enough to protect data:
Beginner's Guide to Encryption: What It Is and How to Set it Up
How mobile device encryption works to protect sensitive data
These are just a few easily found articles which address the encryption need and how to take care of it. Anyone wishing to do more detailed discovery will be easily able to find many more. The above three links will help you understand some of the basics while you begin your more detailed reading.
In the end data integrity is an important business concern. Making sure that if someone inadvertently gets a copy of your data they are not easily able to read or understand it makes good business sense. Taking the time to sort through these issues is good insurance.
Lee K
Photo credit: By Phayzfaustyn (Own work) [CC0], via Wikimedia Commons