It is over twenty five years ago that our company started to actively work in the field of document management. In the early days it was called document imaging as the primary technology involved using high speed scanners to scan and capture images of paper documents for long term storage and retrieval.
Read MoreOffice Document Strategies Blog
Topics: technology tools, document filing, document storage strategy, Hosted document management, data security, Kyocera Canada, digital filing
European Privacy Legislation Has Impact For Canada
Posted by Lee Kirkby on Wed, Jun 6, 2018 @ 07:06 AM
Its been a couple of weeks since the new EU privacy legislation has come into effect. This legislation is the strongest and most defined legislation dealing with the use of data collected through online activities and could easily become a model for what happens in other jurisdictions including Canada and the US.
Read MoreTopics: data security, Canadian Legislation, Canadian IT
Control The Data You Collect Or Face The Peril Of Problems
Posted by Lee Kirkby on Wed, Apr 18, 2018 @ 07:04 AM
Facebook has lost $100B in value — and its money problems...
Facebook's value drops $40B as stock tumbles over data scandal
Facebook value drops by $37bn amid privacy backlash - BBC News
Read MoreTopics: data security, paper filing, Canadian IT, it security
All of the controversy around the issues of the Russian intervention in the US and other country's elections sometimes covers how important cyber security and the ability of IT networks to be secure is to everyday activity. If the general media was only focused on the political consequences of hacking of IT systems we would not hear about how some of the daily things we do are affected.
Some headlines which show Canada is not immune to the issues:
Canadian SMBs hit by ransomware paid out $5.7 million over 12 months: Survey
Interac outlines how it plans to secure Canada's digital identity service
Cyber security a focus of UN Internet governance conference
Canadian firm pays $425,000 to recover from ransomware attack
The costs associated with building systems, acquiring protection software and spending time to keep on top of current threats are all things which we as consumers end up paying for as they get incorporated into the costs of the goods and services which we use.
A recent CNN summary itemizes some of the biggest stories which have occurred including the 145 million accounts from the Equifax hack, the announcement the total of 3 billion Yahoo accounts were hacked in 2013 and closer to home the fact an Ancaster hacker connected to Russians has now pleaded guilty to hacking up to 500 million Yahoo accounts from 2014.
These kinds of events kind of make use glaze over as we figure there is nothing we can do to protect ourselves but we do know that Canadian organizations are forced to spend large amounts to attempt to build protections for us.
We end up having to deal with less convenient systems as things like double authentication security start being applied to our online accounts. Cumbersome conventions which force us to not be able to directly connect to some financial activity without using fairly difficult security procedures frustrate people and lead them to avoid using electronic systems.
Of course the convenience provided by electronic communications including credit and debit transactions hook most of us into continuing to stay connected and to hope that our information will be held secure by the organizations we buy from. Every effort which can be made to help secure online transactions (which include most cash register systems) will pay dividends in consumer confidence hopefully.
Looking ahead to 2018 we can only hope that cyber security will remain a high priority for the legitimate IT industry and that break throughs can occur which will frustrate those who seek to illegitimately use electronic data.
Lee K
Photo credit: By ITSveronica (Own work) [CC BY-SA 4.0 (https://creativecommons.org/licenses/by-sa/4.0)], via Wikimedia Commons
Read More
Topics: data security, Canadian IT, cyber security
Petya | A Malware Attack Combined With Ransomware
Posted by Lee Kirkby on Wed, Jul 5, 2017 @ 07:07 AM
Again the world has had to deal with a range of attacks which involved ransomware but this time with a new twist.
According to an article published by CNET this latest attack included some action which was very poor as ransomware but which really held some serious threat as it ended in an attack which encrypted specific target computers.
Read MoreTopics: data security, ransomware
There can almost never be enough said about how to keep IT networks secure from those who seem bent on creating problems by hacking or stealing information. The first line of defense for every operation is the password protection used by computer users to login to their workstations and applications.
Read MoreTopics: data security, network security, Canadian IT
Google Announces Intent To Open Canadian Region Cloud Centre
Posted by Lee Kirkby on Wed, Mar 15, 2017 @ 08:03 AM
On March 9th Google announced its intention to build a Canadian Region Cloud Centre based in Montreal. This is a significant announcement for Canadian customers and it means that all of the big three hosting services will have Canadian resident facilities to support cloud access from Canada. AWS and Microsoft already offer this option for businesses who wish to connect their hosting and storage to a Canadian location.
Read MoreTopics: cloud computing, data security, Canadian IT
Its the final days of 2016 and we thought it might be a good time to revisit a few of the key stories of this past year before we moved into 2017.
Read MoreTopics: Document, data security, Microsoft
Amazon Web Services - AWS - Opens Canadian Data Centre
Posted by Lee Kirkby on Wed, Dec 14, 2016 @ 08:12 AM
Canadian cloud services users have always had to be cautious in their choice of providers if they want to make sure that their data remains in Canada and subject to Canadian legislative jurisdiction.
Read MoreTopics: Software, cloud computing, data security, Canadian IT
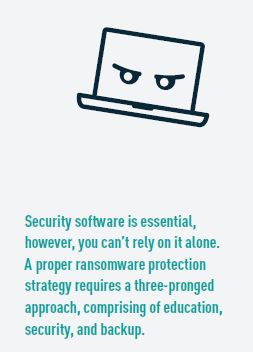
At the risk of appearing to hammer the topic to death it is time to take another crack at warnings about Ransomware Malware attacks.
This time of year is potentially even more challenging to IT managers and users alike as everyone is rushing to get things done before the holiday season really locks in. It means that normal caution can easily be thrown away as people try to clear their email, deal with online activities and perhaps not take that extra two seconds that avoidance can take.
Why now? Simply because the predators can. A recent IT World Canada article outlines how late last month Carlton University had over 3000 of their computers affected, some in research labs by an attempted ransom ware attack. It appears that the IT people got it under control pretty quickly and it was isolated to only a portion of the university network.
It did mean however that thousands of students, faculty and administrators were unable to use the network for a period of time while the details of the attack were sorted through. Eventually, users were advised they could login to their network but many hours of productive time was lost due to the issues.
Another attack in Calgary saw that university paying out $20,000 to the ransomers. Again much time and effort was expended to deal with the circumstances. These are just two of the known instances where Canadian organizations have been impacted by such attacks.
The are for certain many others where users and organizations have not publicized their problems with malware.
For some reason Canada is reported as being more prepared to send compensation for removing the attack when compared to other jurisdictions. Why this would be the case is subject to speculation but unfortunately if it gets known in the perpetrators world it could lead to Canadian targets becoming even more frequent.
What do you do?
The first line of defense is the users on the network. Encouraging everyone to take a little time to investigate whether an email from an unfamiliar source is legit. If a user is not CERTAIN of the sender then the default response should be to NO OPEN IT. Either delete it and take the chance someone legit has to try again, or contact IT support to have it checked out.
Read MoreTopics: data security, network security, IT Scams