Microsoft is planning to release the commercial version of Windows 10 this fall. Two days ago they released the Windows 10 Preview which will permit some users to test out the new system.
Read MoreOffice Document Strategies Blog
Microsoft Announces New Security Features For Windows 10
Posted by Lee Kirkby on Wed, Apr 29, 2015 @ 08:04 AM
Topics: data security, Windows 10, office technology
Canadian Government IT Data Breaches Up Reports Privacy Commissioner
Posted by Lee Kirkby on Wed, Nov 5, 2014 @ 07:11 AM
Topics: data security, network security
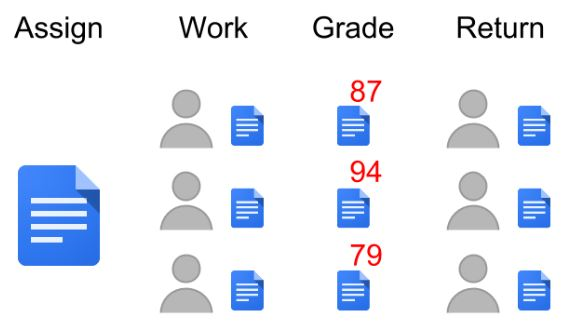
Classroom By Google Docs Shows Altered Paper Workflow Potential
Posted by Lee Kirkby on Wed, Oct 22, 2014 @ 07:10 AM
Topics: workflow processes, cloud computing, data security, Kyocera Canada
Topics: cloud computing, Hosted document management, data security, Canadian Legislation
5 Business Process Challenges That Could Have Been Avoided
Posted by Lee Kirkby on Wed, Sep 10, 2014 @ 11:09 AM
One of the frustrations we experience is when we see clients doing things that could have been avoided with a little consultation in advance and with some pre planning. Since our role is helping clients to avoid issues with their critical business documents, when we see them facing problems we know could have been solved with some simple and early action, it is frustrating.
Topics: network server, document filing, document storage strategy, document management, server software, network backup, business processes, data security
Making Productive Business | Microsoft Small Business Newsletter
Posted by Lee Kirkby on Wed, Aug 6, 2014 @ 08:08 AM
One of the tools that can help manage a business is to read material being produced by companies which have a stake in the small business marketplace. This is one of the primary purposes of this blog as we focus on helping business people learn about our area of expertise, Office Documents. This involves many areas of specialization and we use the resources of many of our suppliers to find ideas and to support our efforts.
Topics: technology tools, cloud computing, network backup, business processes, data security
Topics: cloud computing, document storage strategy, data security
"Last year was by far the worst ever for security, with 2,164 incidents that exposed 822 million records, according to one security report."
In his recent ITWorldCanada article this is only one of many striking comments made by author Andrew Brooks. He goes on in the article to outline nine key etiquette steps which can help you protect your reputation even if a breach occurs. Some are obvious, such as disclose what has happened and what is at risk, as well as focusing on looking after your customers and any others who may be affected by the breach.
Topics: business processes, data security, network security