As anyone who is looking for a multifunction printer (MFP) knows there are hundreds of options you could choose from. Of course not all of them will be in your particular budget so that is one tool for narrowing your choices but there are also other considerations which you must think about.
Read MoreOffice Document Strategies Blog
Lee Kirkby
Recent Posts
Topics: Multifunction Printer, MFP, colour multifunction, Multifunction Printer support
One of the key parts of any IT technology strategy in a business is having the right kinds and levels of support available to underpin your operations. The days are long gone where every organization can have the knowledge base and the personnel in place to be able to handle every IT related eventuality.
When you think of all of the components of the complexity of your IT systems being able to understand who and how your systems are being supported is critical to your design and comfort level.
Software
Every business has several levels of software which are important to the business.
- ERP or business operations software
- Network operating systems with components like backup, email security, data management structures
- Cloud based software pieces including related storage and backup
- Communications software which may also include phone system software
Hardware
- Hardware components including workstations, point of input devices like physical security systems, server components, connectivity components like routers, switches and wireless infrastructure
- Mobile hardware devices including computers and smart tools like tablets and phones
- Scanning hardware whether stand alone or networked
- Print hardware including multifunction print devices and tools
- Related hardware management tools and supplies
Communications
There are several streams of communications systems that every business uses and these include phone systems, email systems, online and in house business transaction systems like shopping stores and inventory management.
Group meeting chat software and tools are also a piece of this area and for some businesses have become the primary ways for widely dispersed employee groups to meet and interact.
The whole network system infrastructure is often a big part of the communication system as cloud based services and tools become more integrated and prevalent.
Production systems
For some businesses a big part of their IT environment is dominated by production related resources. This is a critical yet specialized part of operations such as manufacturing and other process type industries.
Even in service industries like restaurants, health services, education and others this kind of infrastructure can become a big part of the operation.
Where is support coming from?
Read MoreTopics: IT network, IT support, it, IT connectivity
Store Transaction Documents Electronically Instead of As Paper
Posted by Lee Kirkby on Wed, May 8, 2019 @ 08:05 AM
I recently was dealing with a reservation for parking at the airport for a trip and I was offered two options for capturing my confirmation; printing it out or storing electronically on my phone or computer. This is a pretty common occurrence these days in all forms of consumer transactions. "Do you want an emailed receipt' shows up at the cash register at Home Depot every time. Other interactions like banking, ticket purchases and airplane boarding passes all offer an electronic option instead of printing out a copy.
Read MoreTopics: document management, office document strategy, business processes, digital tools, digital filing, e-signatures, AP Automation, automation
Business is always a challenging contest of dealing with the urgency of each day while keeping an eye on the future to ensure that problems do not occur because important decisions are put off.
Read MoreTopics: office technology, it security
March 12 2019 was a significant birthday for the current world of communications, promotion, information exchange and research. It was on this date in 1989 that the World Wide Web was nominally launched and opened to the world.
Of course in the early years there was limited growth and it was not until the early part of the 1990s that it became available to the general public, although it was starting to be used by academia and some corporate organizations. Personally I recall the first instances were I was able to access 'the web' by using an account granted through McMaster University and working with a dial up modem over phone lines at speeds around 300 baud. It was a text based world at that time and you didn't get images or video due to the very low connections speeds.
I migrated to my first personal commercial account through Net Access in 1994 being one of their early customers. Still access was through pretty slow dial up connections but it could be instant and cover long distances at no additional cost.
Contrast this to the norm for communications in those days with phone, mail and fax being the most dominant forms available. Before fax became available telex was the key quick communication for governments and larger corporations. For the public it really was phone and mail which dominated communications.
Two generations now know only the WWW world
As we move from the last part of the second and into the third decade of the twenty first century there are now two full generations who have grown up knowing only the instant world of the World Wide Web and the millions of enhancements it has undergone over its thirty years of existence.
Read MoreTopics: technology tools
Sometimes we forget that many of the things which happen every day in business rely upon a basic trust in the performance of those around us. It could be colleagues and others from our team, suppliers and their ability to get us the products we use, in the basic infrastructure around us that facilitates our activities or it could be customers who are consistent in their requests for us to perform.
Read MoreTopics: Environment
ScanSnap ix500 | Long Standing Standard For Distributed Scanning Reaches End Of Life
Posted by Lee Kirkby on Wed, Feb 20, 2019 @ 07:02 AM
The favourite affordable Fujitsu Scansnap scanner of almost every business is being retired. The darling and often revered by Accounting offices, Lawyers, Custom brokers and other busy offices etc. The ScanSnap ix500 is being phased out.
Read MoreTopics: workflow processes, Scanning, document filing, digital tools
Microsoft Security Patch Breaks SMB Scanning On MFPs
Posted by Lee Kirkby on Wed, Feb 6, 2019 @ 06:02 AM
Reports are coming in that many older functioning MFPs from virtually every brand are having difficulty with SMB scanning due to an upgrade that Microsoft has released which affects the older versions of SMB (V0 & V1). The upgrade corrects a security problem which is a good thing but for networked MFPs from Kyocera, Ricoh, Konica Minolta, Canon, Toshiba, Sharp, Samsung and other brands, it can interfere with the functioning of their scanning operations.
Read MoreTopics: Multifunction Printer, Scanning, MFP, photocopier, Multifunction Printer support, Windows 10, Microsoft, it security
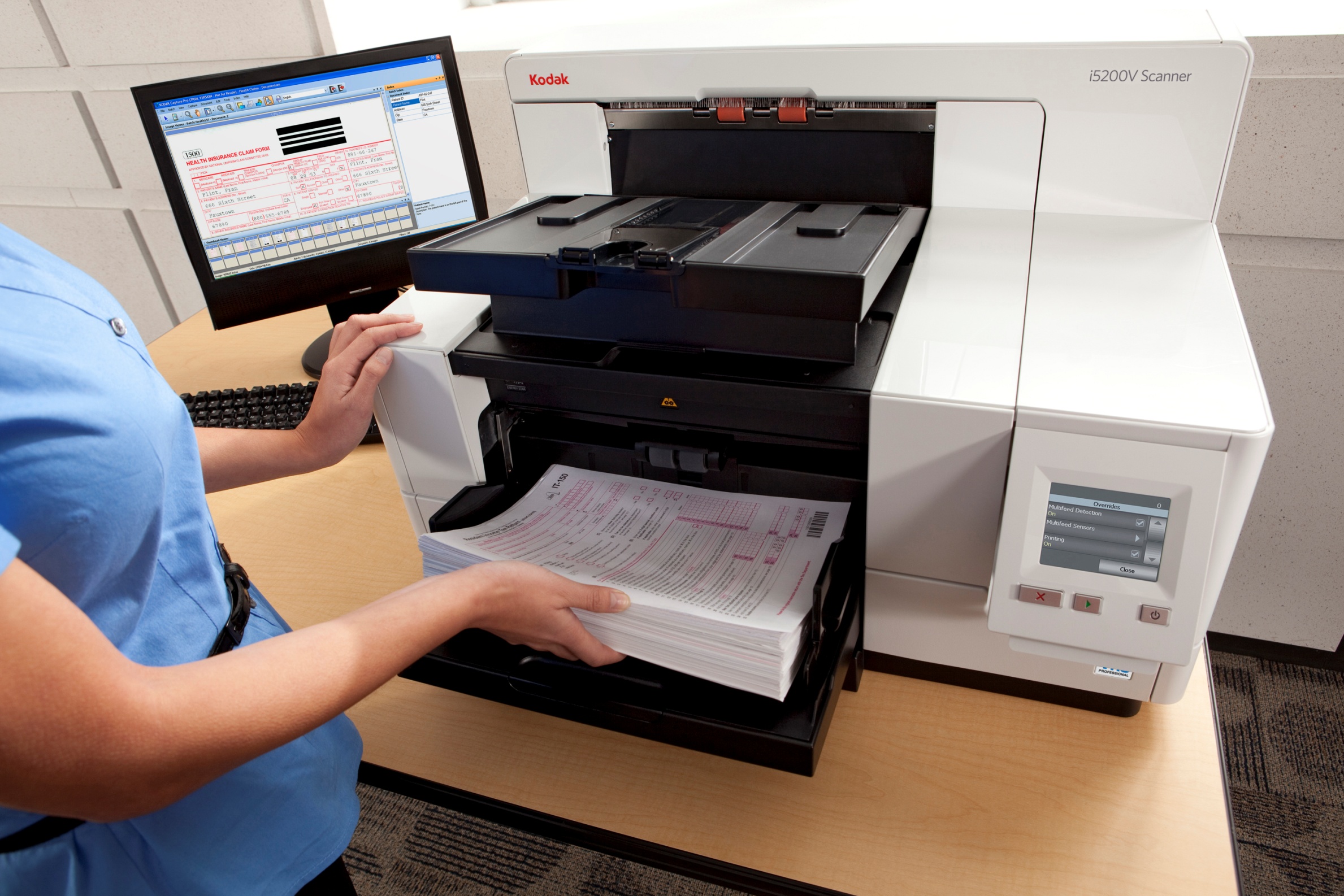
Government of Canada Reliability Certified Scanning
Posted by Lee Kirkby on Wed, Jan 23, 2019 @ 08:01 AM
Leppert has provided outsourced scanning for hundreds of clients over the past 23 or so years. Through the use of in house scanning systems this service has assisted many clients to reduce the amount of paper they have to store, by converting to more convenient digital format's like searchable PDF. In many instances we are also able to capture key meta data from these paper records to aid in improved document retrieval.
Read MoreTopics: Scanning, document filing, document storage strategy, digital filing