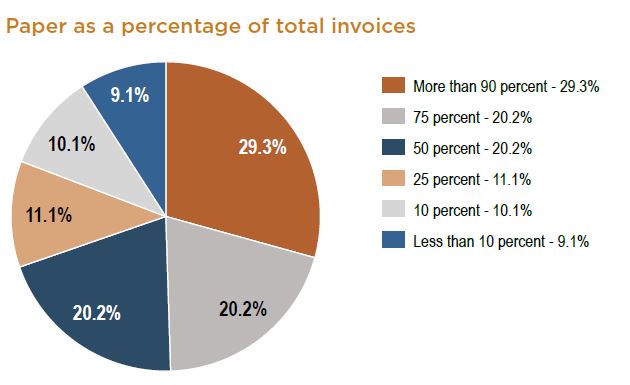
In a 2014 study or the levels of use of Account Payable automated systems respondents indicated that paper invoices remain a big part of their payables operations. 70 percent said that at least 50 percent of their invoices are still being tendered in paper format and less than 9 percent said paper invoices are less than 10 percent of their total volume.
Read MoreOffice Document Strategies Blog
Lee Kirkby
Recent Posts
13 Reasons To Implement Automated AP Processing
Posted by Lee Kirkby on Wed, Sep 21, 2016 @ 09:09 AM
Topics: AP Automation
Kycoera PinPoint Scan Enhances MFP Scanning - Leppert blog
Posted by Lee Kirkby on Wed, Sep 14, 2016 @ 08:09 AM
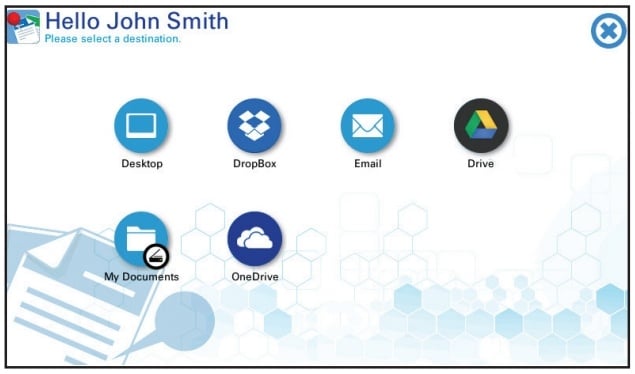
If you need to improve productivity and find a simple way to Scan to your PC, Mac locally or in Cloud Apps like Microsoft 365 (Office 365) OneDrive, Google Drive, Dropbox or others, then this could be the App you have been looking for.
Most modern MFPs (multi-function printers) include the capability of basic network scanning in their setup. Using simple scan to email, or scan to folder systems, they make it possible for users to send and convert paper documents to images like PDF format. This capability provides many benefits to your users in the 'war on paper' but still leads to manual steps for filing or renaming, making the systems not as efficient for frequent work.
Read MoreTopics: Scanning, document management, MFP, Kyocera copier, Paperless office, office technology
Automated Accounts Payable And Invoice Processing Generate Savings and Gain Productivity
Posted by Lee Kirkby on Wed, Aug 31, 2016 @ 18:08 PM
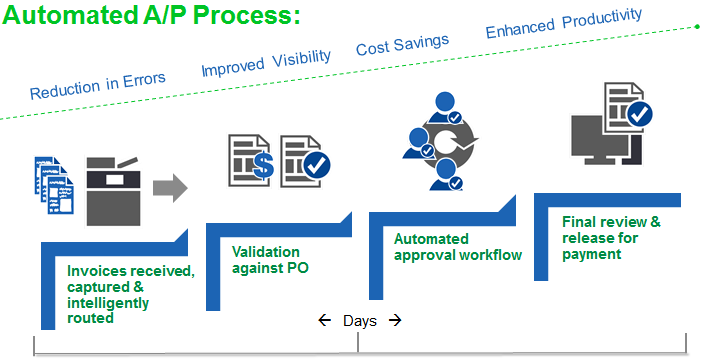
One of the great benefits of technology available to businesses today is being able to automate what was commonly a routine process which in a manual paper based world has taken extra time.
Read MoreTopics: workflow processes, running costs, cloud computing, Scanning, document filing, document storage strategy, software tools, business processes, paper filing, Paperless office, Less paper office, digital tools, AP Automation
Your 3 Choices of Canadian Postage Meter Companies
Posted by Lee Kirkby on Fri, Aug 26, 2016 @ 00:08 AM
FrancoTyp Postalia
Neopost (now called Quadient)
And the oldest Pitney Bowes
Many Canadian businesses don't realize that they have a choice of postage meter companies when they are looking to rent a postage machine.
Topics: Postage meter, postage rates, mailing equipment, meter rentals, postage machine
Buying a Postage Meter In Canada - Three Choices
Posted by Lee Kirkby on Fri, Aug 26, 2016 @ 00:08 AM
If you are buying or renting a postage meter in Canada you essentially have three choices of manufacturer. Many people think that there is only one meter rental company authorized to sell postage equipment in Canada. In fact there are three companies who are the manufacturers of equipment and who have approval from Canada Post for providing postage meters. These companies in alphabetical order are: Francotyp-Postalia Canada, Neopost Canada and Pitney Bowes Canada.
Topics: Postage meter, postage rates, mailing equipment, Mailing, Postage, mailing machines, postage machines, meter rentals, postage machine
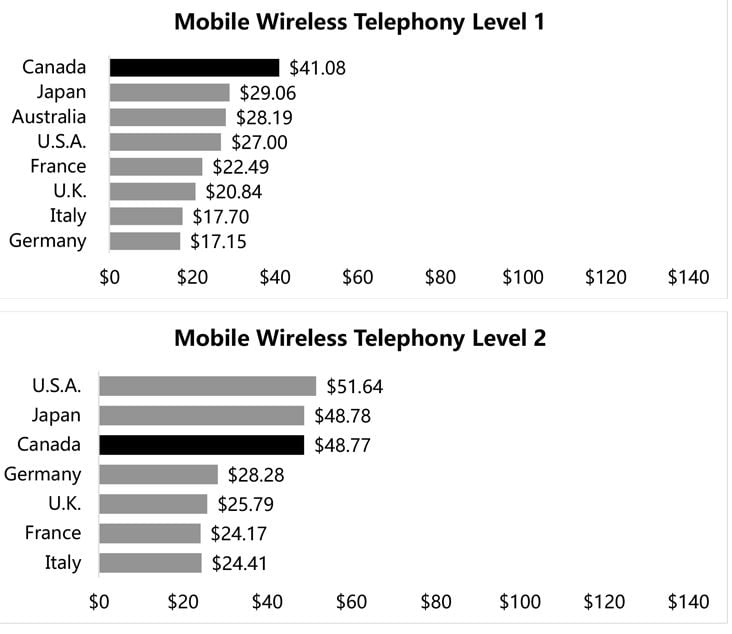
Canadian Telecommunications Are Generally Pricey
Posted by Lee Kirkby on Tue, Aug 23, 2016 @ 08:08 AM
One of the things that most Canadians take for granted is the ability to communicate broadly both internally and internationally. In order to do this we spend significant budgets on wired, wireless, broad band wireless and wired (fixed) internet and finally on TV services.
Read MoreTopics: Canadian Pricing
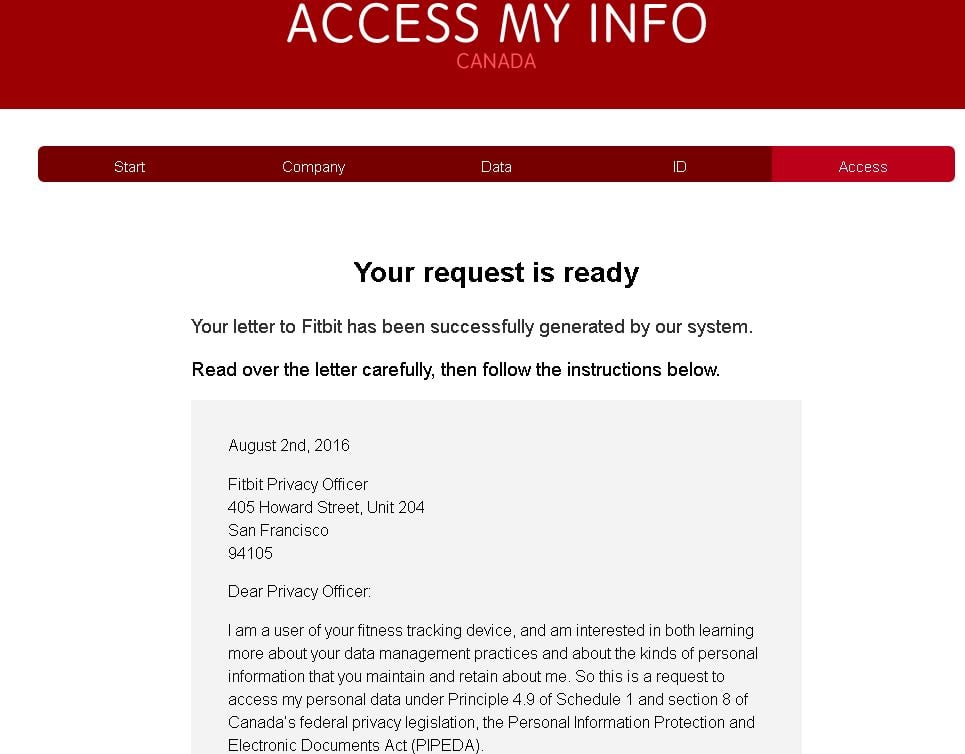
One of the things we all know about our social media and internet activity is that it creates a large volume of data for the businesses who's tools we use.
Read MoreTopics: privacy
One of the things that drives print manufacturers to improve their equipment offerings is the ability to have the newer units tested for performance by the independent testing labs. After some time it is harder to get the interest of customers and potential adopters as there is always a new crop of equipment being introduced by someone in the industry.
Read MoreTopics: MFP, Printer, Kyocera copier, Kyocera Canada
Ever since the early days of the photocopier and now the connected printer there have been unscrupulous players who have promoted and sold toner for massive premiums over the real retail price. There are a number of ways the scams work but the most common we see involve phone contacts to unwitting potential targets.
Read MoreTopics: toner, Multifunction Printer support
Personal Information And Important Stored IT Data
Posted by Lee Kirkby on Wed, Jun 29, 2016 @ 08:06 AM
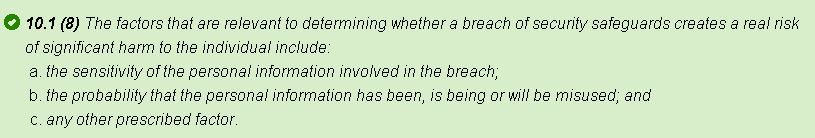
One of the biggest issues for IT security and business operations is keeping their data safe and secure.
There is a massive amount of material available about data backup, building redundancy for continued operations and how to teach people to be careful in providing access to company data. In spite of all of the effort and expense that is put into this field there are still too many data breaches.
Read MoreTopics: data security, digital tools